The digital security landscape has fundamentally shifted, as the details regarding the ai hacking found google report are finally emerging. Security researchers have long warned that artificial intelligence could one day accelerate cyberattacks. That day appears to be here, and the implications are massive for global cybersecurity.
In 2026, technology companies and enterprises face a new breed of threat actors. These criminals are no longer relying solely on manual coding to exploit systems. Instead, they are leveraging advanced models to scale their operations.
Understanding the Scope of the ai hacking found google report
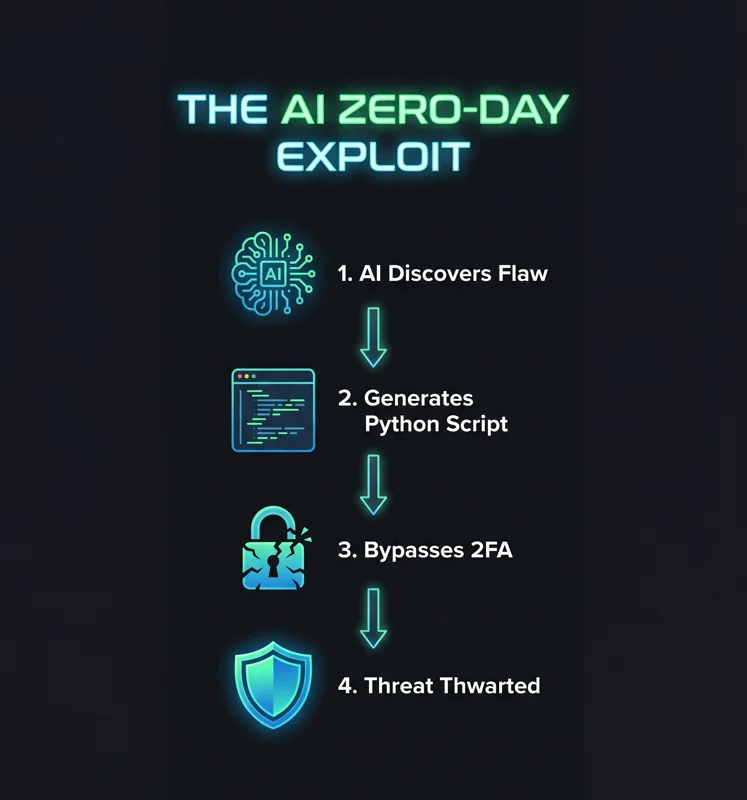
Google has identified what may be the first known case where cybercriminals used AI to discover and weaponize a previously unknown zero-day vulnerability. According to the ai hacking found google report, this marks a dangerous escalation in the cyber arms race.
Prominent cyber crime threat actors partnered to identify a complex bug in a Python script. This specific vulnerability would allow attackers to bypass two-factor authentication (2FA) on a popular open-source system. The severity of this cannot be overstated.
| Threat Component | Description |
|---|---|
| Attack Vector | AI-generated Python exploit script. |
| Target | Open-source 2FA login logic. |
| Discovery Status | Thwarted and disclosed to vendor. |
“There’s a misconception that the AI vulnerability race is imminent. The reality is that it’s already begun.”
The tech giant based its assessment on characteristics common in machine-generated scripts. These included overly explanatory comments in the code and a made-up severity rating for the bug.
Deep Dive into the ai hacking found google report Vulnerabilities
Advanced machine learning models are getting noticeably better at finding subtle security weaknesses in software. These are vulnerabilities that conventional cybersecurity tools often fail to catch. The ai hacking found google report highlights this critical blind spot.
In the documented zero-day example, the model appeared to identify a hidden trust assumption in the software’s login logic. This flaw could be exploited to bypass security protections seamlessly.
To understand the full magnitude of this, you must look at the official data. You can read more from the Google Threat Intelligence team regarding these emerging digital threats.
| Malware Type | Functionality |
|---|---|
| PromptSpy | Autonomously navigates Android devices. |
| Zero-Day Scripts | Bypasses 2FA via hidden trust assumptions. |
| Exploit Validators | Tests thousands of software flaws simultaneously. |
Real-World Implications of the ai hacking found google report
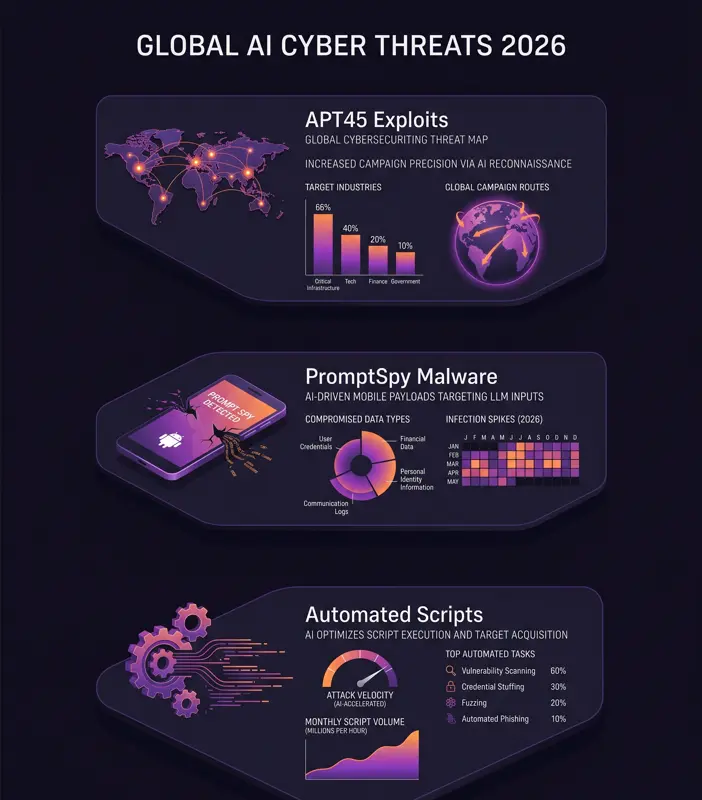
The global threat landscape is evolving rapidly. The AI-assisted exploit was just one of several cases uncovered in recent months. The ai hacking found google report emphasizes a growing interest among nation-state hackers.
North Korean and Chinese state actors are currently experimenting with artificial intelligence in a variety of ways. In one case, researchers found APT45, a North Korean military group, using automation to test thousands of exploits.
“For every zero-day we can trace back to AI, there are probably many more out there.”
Furthermore, the discovery of malware dubbed PromptSpy shows the versatility of these attacks. This malware interprets on-screen activity and generates commands in real time.
| Nation-State Group | Observed Activity in 2026 |
|---|---|
| APT45 (North Korea) | Validating thousands of software exploits. |
| Unidentified Cybercriminals | Weaponizing Python zero-day flaws. |
U.S. technology companies are increasingly grappling with how to prevent their more sophisticated models from being abused. This is a crucial defense initiative for 2026 and beyond.
Frequently Asked Questions on the ai hacking found google report
What is the main finding of the ai hacking found google report?
The ai hacking found google report reveals that cybercriminals successfully used artificial intelligence to discover and weaponize a zero-day vulnerability in an open-source system.
How does the AI exploit bypass security?
The model identified a hidden trust assumption in the software’s login logic, allowing attackers to bypass two-factor authentication (2FA) protections.
Are nation-state hackers involved in these attacks?
Yes. The report highlights that state-backed groups, such as North Korea’s APT45, are actively using machine learning to validate thousands of exploits targeting software flaws.
How did Google identify the code as AI-generated?
Researchers noticed characteristics common in machine-generated scripts, such as overly explanatory comments, made-up severity ratings, and specific coding patterns.
What is PromptSpy?
PromptSpy is a newly discovered malware that uses advanced models to autonomously navigate Android devices by interpreting on-screen activity.
Was the 2FA exploit successful?
Fortunately, the attempt to exploit the unidentified open-source system was thwarted, and the flaw has been disclosed to the vendor.
Why is this ai hacking found google report significant for 2026?
It confirms that the theoretical threat of machine-accelerated cyberattacks is now a practical reality, changing how cybersecurity defenses must be built.
Disclaimer: This article is for informational purposes only and does not constitute professional cybersecurity advice. Ensure all systems are updated and consult with IT security professionals for network defense.