The cybersecurity landscape is on high alert today as the u s government warns of severe copyfail bug affecting major versions of linux. This unprecedented vulnerability, officially designated as CVE-2026-31431, has caught enterprise IT defenders completely off-guard. With functional exploit code publicly released and actively circulating among malicious hacking groups, the risk to global digital infrastructure is both immediate and severe. Security researchers are scrambling to help organizations assess the damage, while system administrators face a stressful race against time to implement critical updates across massive data center environments.
Understanding the Massive Blast Radius of CopyFail
The core issue with this Linux kernel vulnerability is its staggering reach. The bug was discovered in Linux kernel versions 7.0 and earlier, meaning it impacts systems that have been the backbone of the internet for years. While the Linux kernel security team was notified in late March 2026 and patched it within a week, the complex nature of open-source ecosystems means these updates have not fully trickled down. Operating systems running in critical enterprise settings, managing everything from banking databases to cloud host architectures, remain heavily exposed.
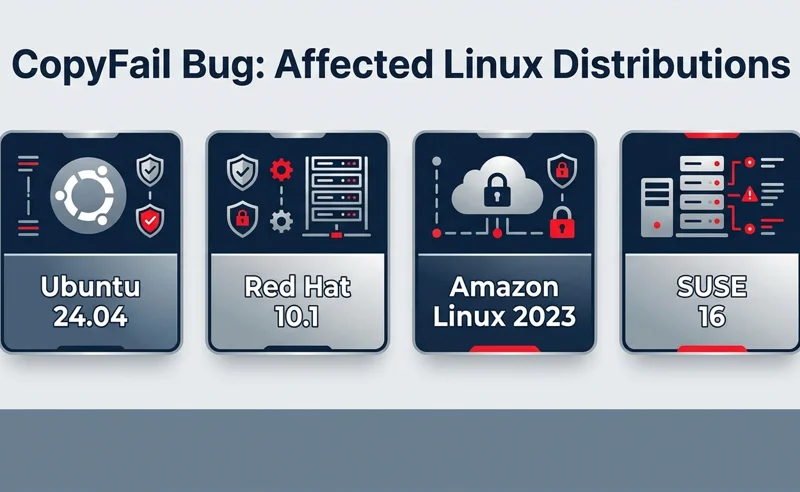
The CopyFail vulnerability possesses an unusually big blast radius, compromising almost every modern Linux distribution shipped since 2017.
Security firm researchers who initially discovered the flaw have confirmed that a short, simple Python script is all it takes to root these distributions. Whether an enterprise is running Red Hat, Ubuntu, Amazon Linux, or Debian, the underlying kernel flaw leaves the door wide open for devastating intrusions.
| Linux Distribution | Version Verified as Vulnerable | Impact Severity |
|---|---|---|
| Ubuntu | 24.04 (LTS) and older | Critical |
| Red Hat Enterprise Linux | 10.1 and older | Critical |
| Amazon Linux | 2023 and previous | Critical |
| SUSE | 16 and older | Critical |
The Technical Mechanics of CVE-2026-31431
To comprehend why the U.S. government is issuing urgent alerts, one must understand the technical failure causing the vulnerability. The bug earned the moniker “CopyFail” because a crucial component within the Linux kernel fails to properly copy data during specific internal operations. The kernel, being the foundational core of the operating system, has absolute control over device hardware and memory.
When this data copying process fails, it corrupts sensitive memory regions within the kernel itself. A local attacker can manipulate this corruption to achieve a privilege escalation exploit. By exploiting this memory flaw, a user with standard, highly restricted permissions can elevate their status to full administrative control, leading to a total root access compromise.
A successful CopyFail exploit transforms a harmless, limited user account into an all-powerful root administrator, stripping away all system defenses in seconds.
| Vulnerability Phase | Attacker Action | System Result |
|---|---|---|
| Initial Access | Gains low-level user access | Limited environment entry |
| Exploit Execution | Runs Python CopyFail script | Kernel memory corruption |
| Takeover | Piggybacks kernel permissions | Full root authority granted |
Attack Vectors: Chaining and Supply Chain Risks
While the CopyFail bug cannot typically be exploited remotely over the internet by itself, it becomes a devastating weapon when chained with other vulnerabilities. For example, if an attacker uses a minor web application flaw to gain basic shell access to a server, they can immediately deploy the CopyFail script to seize total control. This chaining technique is highly favored by Advanced Persistent Threat (APT) groups.
Furthermore, experts warn of severe supply chain implications. Malicious actors could compromise an open-source developer’s repository, injecting the CopyFail trigger into legitimate software updates. This method could infect thousands of downstream enterprise servers simultaneously. To stay informed on these evolving threats, administrators should regularly consult the Cybersecurity and Infrastructure Security Agency.
Urgent Mitigation and Patch Management
Addressing this crisis requires immediate and aggressive cybersecurity patch management. Since standard security perimeters do not protect against local privilege escalation once an intruder is inside, updating the kernel is the only definitive fix.
Delaying kernel updates in the face of active CopyFail exploitation is akin to leaving the master keys to your data center unguarded.
Organizations must prioritize identifying all instances of Linux running within their infrastructure, including containerized environments like Kubernetes, which also rely on the shared host kernel. Applying the patches released by distribution maintainers should bypass standard testing delays due to the critical severity of this active threat.
| Step | Action Required | Priority Level |
|---|---|---|
| 1. Audit | Scan all network assets for kernel version 7.0 or older. | Immediate |
| 2. Patch | Apply official vendor updates to secure the kernel. | Immediate |
| 3. Reboot | Restart servers to ensure the new kernel is actively running. | High |
| 4. Monitor | Watch system logs for unauthorized user privilege escalations. | Ongoing |
Frequently Asked Questions

What exactly is the CopyFail bug?
CopyFail is a severe security vulnerability found in Linux kernel versions 7.0 and earlier that fails to properly copy data, allowing limited users to gain full administrator privileges.
Can this bug be exploited remotely?
Not on its own. An attacker first needs basic access to the system, which they can obtain by chaining CopyFail with another internet-facing vulnerability.
Which versions of Linux are affected?
Almost every modern distribution shipped since 2017 is impacted, including popular enterprise versions like Ubuntu, Red Hat, SUSE, and Debian.
How did this vulnerability get its name?
It is named CopyFail because the core issue stems from the Linux kernel failing to execute a required data copying process properly, leading to memory corruption.
Are container environments like Kubernetes at risk?
Yes. Because Kubernetes relies on the underlying Linux host kernel, containers running on vulnerable nodes can be compromised.
What should system administrators do immediately?
Administrators must conduct a full infrastructure audit, apply the latest security patches provided by their Linux vendors, and reboot systems to load the secured kernel.
Is the vulnerability actively being used by hackers?
Yes, the U.S. government has confirmed that the exploit is being actively used in the wild in malicious hacking campaigns.
Disclaimer: This article is for informational purposes only…

![An infographic highlighting three key facts about [Insert Topic], including [Insert brief hint about Fact 1], [Insert hint about Fact 2], and [Insert hint about Fact 3]](https://mobileservicescenter.com/wp-content/uploads/2026/05/featured_5f9911.webp)