A critical linux cryptographic code flaw has sent shockwaves through the cybersecurity community in 2026, offering threat actors an unprecedented, lightning-fast route to total system takeover. Dubbed “Copy Fail” and officially tracked as CVE-2026-31431, this severe vulnerability stems from a logic error deep within the Linux kernel. Developers across all major distributions are currently scrambling to ship patches, as the exploit allows an unprivileged local user to escalate their permissions and gain root access using remarkably little code.
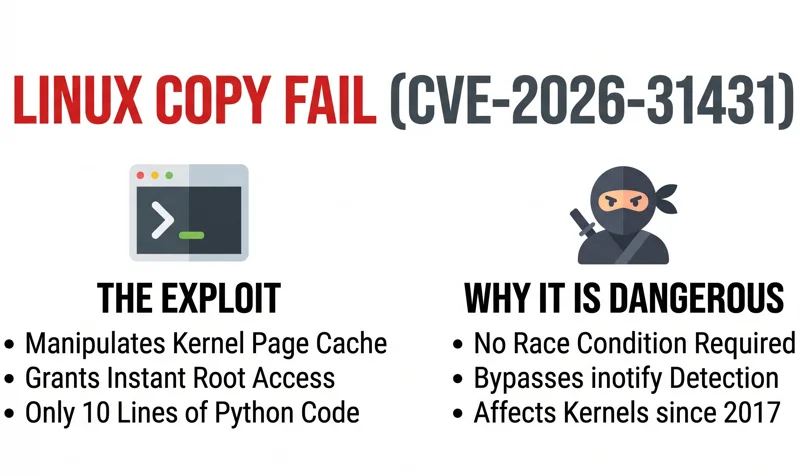
The discovery of this Local Privilege Escalation (LPE) flaw highlights the continuous hidden dangers lurking in foundational open-source code. Rated at a High severity score of 7.8 out of 10, Copy Fail is not just a theoretical concept; it is highly weaponizable. Security researchers have demonstrated that a mere 10-line Python script is all it takes to compromise almost all Linux distributions released since 2017.
| Vulnerability Detail | Information |
|---|---|
| CVE Identifier | CVE-2026-31431 |
| Common Name | Copy Fail |
| Vulnerability Type | Local Privilege Escalation (LPE) |
| CVSS Severity Score | 7.8 (High) |
The Mechanics of Copy Fail: A Stealthy Page Cache Manipulation
Understanding how this linux authencesn cryptographic flaw operates requires looking at how the operating system handles file execution. According to a detailed writeup by the security firm Theori, the vulnerability specifically exists within the kernel’s authencesn cryptographic template. An unprivileged local attacker can exploit this logic flaw to write four controlled bytes directly into the page cache of any readable file on the Linux system.
Because the Linux kernel reads from the page cache when loading a binary, modifying this cached copy essentially alters the binary in memory just as it is being executed. The brilliance—and danger—of this exploit is its stealth. Since the modification happens in the cache rather than on the disk, it entirely bypasses standard file system event monitoring tools like inotify, leaving security teams completely blind to the intrusion.
“The proof of concept exploit is terrifyingly elegant: a 10-line, 732-byte Python script capable of editing a setuid binary to achieve instant root access on virtually any modern Linux distribution.”
Security analysts have compared Copy Fail to legendary Linux bugs like Dirty Cow and Dirty Pipe. However, the discoverers note a chilling distinction: Copy Fail is far more broadly applicable and does not require the attacker to win a complex “race condition” to succeed, making it much more reliable for malicious actors.
| Exploit Comparison | Copy Fail (2026) | Dirty Cow / Dirty Pipe |
|---|---|---|
| Race Condition Required? | No | Yes (Dirty Cow) |
| Detection Evasion | High (Bypasses inotify) | Moderate |
| Execution Complexity | Very Low (10 lines of Python) | High to Moderate |
Widespread Impact: Containers and Multi-Tenant Threats
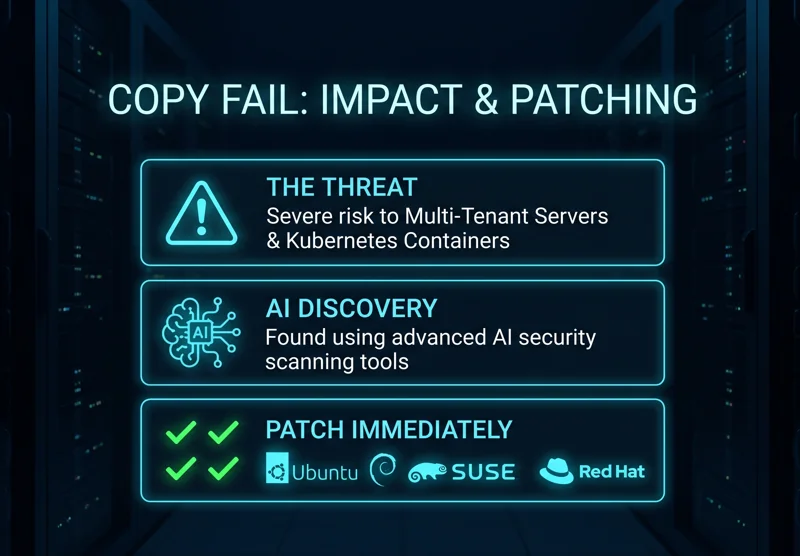
While Copy Fail is categorized as a Local Privilege Escalation—meaning an attacker must already have some form of access to the machine—it is a critical piece of the puzzle for advanced cyberattacks. If an attacker chains this flaw with a Remote Code Execution (RCE) vulnerability in a web application, a compromised SSH credential, or a malicious CI runner, the results are catastrophic.
Theori researchers have issued stark warnings for enterprise environments. The vulnerability represents a massive threat to multi-tenant Linux systems and shared-kernel containers. Specifically, it acts as a container escape primitive. Because the page cache is shared across the host OS, a compromised Kubernetes node could allow an attacker to break out of their isolated container and infect the entire host infrastructure.
“For organizations relying on shared-kernel architectures and Kubernetes, failing to patch CVE-2026-31431 immediately is akin to leaving the vault door wide open.”
The Rise of AI in Discovering Zero-Days
One of the most fascinating aspects of CVE-2026-31431 is how it was found. Theori researcher Taeyang Lee uncovered the vulnerability with the assistance of Xint Code, the company’s proprietary AI security scanning software. This marks a turning point in cybersecurity for 2026, where AI-powered flaw-finders are drastically accelerating the rate of vulnerability disclosure.
Dustin Childs, head of threat awareness for Trend Micro’s Zero Day Initiative, recently commented on this trend. He noted that the massive surge in bug reports across major tech companies is directly correlated to security teams deploying advanced AI hunting tools. The influx of reports has been so overwhelming that organizations like the Internet Bug Bounty (IBB) temporarily suspended awards to restructure their management protocols. For ongoing updates on known vulnerabilities, administrators should frequently consult the National Vulnerability Database.
| Linux Distribution | Patch Status for CVE-2026-31431 |
|---|---|
| Ubuntu | Patches Issued |
| Debian | Patches Issued |
| SUSE | Patches Issued |
| Red Hat Enterprise Linux | Patches Issued (After initial deferment) |
“The AI arms race in cybersecurity has officially begun; defenders are using artificial intelligence to patch foundational flaws before attackers can train their own models to exploit them.”
Conclusion: Update Your Systems Immediately
The revelation of the Copy Fail bug serves as a grim reminder that even mature, widely scrutinized open-source projects can harbor devastating logic flaws. System administrators must prioritize applying the latest kernel patches from their respective distributions immediately. With exploit code readily available and highly reliable, unpatched multi-tenant servers and containerized environments remain at critical risk.
Frequently Asked Questions
What is the Copy Fail vulnerability?
Copy Fail (CVE-2026-31431) is a Local Privilege Escalation (LPE) flaw in the Linux kernel that allows an unprivileged user to gain root access by manipulating the system’s page cache.
How does the linux cryptographic code flaw work?
The vulnerability exists within the kernel’s authencesn cryptographic template. It allows an attacker to write four controlled bytes into the page cache of a readable file, effectively altering the binary in memory during execution.
Is CVE-2026-31431 remotely exploitable?
No, it is not remotely exploitable on its own. An attacker must already have local access to the system. However, it can be chained with a remote exploit (like a web vulnerability) to gain full system control.
What systems are affected by this exploit?
The flaw affects almost all major Linux distributions released since 2017, making it a widespread threat to servers, desktops, and containerized environments.
How does it compare to Dirty Cow?
While similar in impact (gaining root access), Copy Fail is considered more reliable because it does not require the attacker to win a complex race condition, and it evades file system monitoring tools like inotify.
Who discovered the Copy Fail flaw?
The vulnerability was identified by Taeyang Lee, a security researcher at Theori, utilizing the company’s advanced AI security scanning software known as Xint Code.
Are patches available for my Linux distribution?
Yes, major distributions including Ubuntu, Debian, SUSE, and Red Hat have already issued kernel updates to patch CVE-2026-31431. Administrators should update their systems immediately.
Disclaimer: This article is for informational purposes only. System administrators should consult their official Linux distribution security advisories for the most accurate patching guidelines and technical remediation steps.


