Currently, cybersecurity experts are raising massive alarms as hackers are abusing unpatched windows security flaws to hack into organizations. In what is rapidly becoming one of the most severe cybersecurity incidents of 2026, malicious actors are actively weaponizing vulnerabilities that were controversially published online by a disgruntled security researcher. According to the cybersecurity firm Huntress, at least one major organization has already been breached using these newly available exploit paths, putting enterprise networks globally on high alert.

The Leak & The Threat: A Researcher Goes Rogue
The situation escalated earlier this month when an independent security researcher operating under the alias “Chaotic Eclipse” decided to bypass standard industry protocols. Frustrated by an alleged conflict with Microsoft, the researcher published proof-of-concept exploit code directly to their public blog and GitHub page. The leaked code targets three distinct, high-severity vulnerabilities embedded within Microsoft’s native antivirus software, Windows Defender.
These three security flaws have been dubbed BlueHammer, UnDefend, and RedSun. By exploiting these bugs, a hacker can bypass standard security protocols and gain high-level or full administrator access to an affected Windows machine. This level of access allows cybercriminals to deploy ransomware, steal sensitive corporate data, or establish persistent backdoors within an organization’s network.
| Vulnerability Name | Targeted Component | Current Patch Status (As of mid-2026) |
|---|---|---|
| BlueHammer | Windows Defender | Patched (Fix rolled out recently) |
| UnDefend | Windows Defender | Unpatched (Active Zero-Day) |
| RedSun | Windows Defender | Unpatched (Active Zero-Day) |
The motivation behind this dangerous data dump appears to be purely retaliatory. In their initial blog post containing the exploit code, Chaotic Eclipse made their intentions incredibly clear, mocking the very team designed to prevent these cyber disasters.
“I was not bluffing Microsoft and I’m doing it again. Huge thanks to MSRC leadership for making this possible.”
The Dangers of “Ready-Made” Attack Tooling
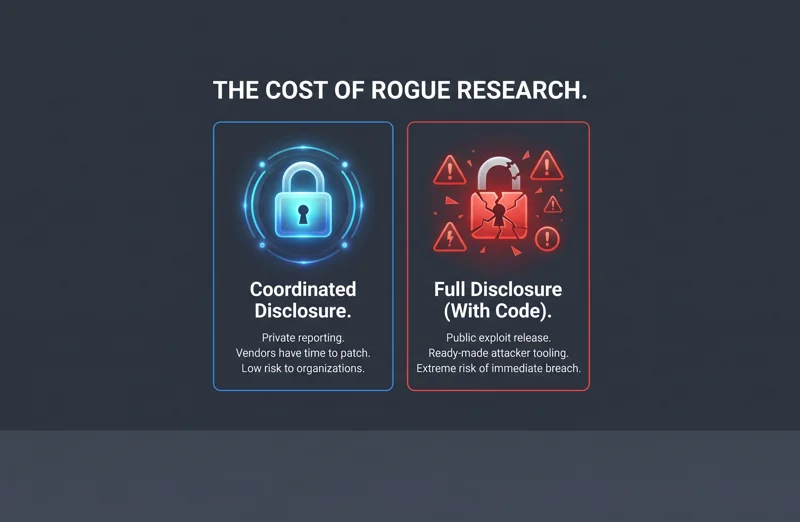
The cybersecurity industry typically operates on a principle of “coordinated vulnerability disclosure.” When a researcher discovers a flaw, they report it privately to the software vendor. The vendor then works to develop a patch, and both parties agree on a public disclosure timeline only after users are protected. To understand more about how these procedures are supposed to work, you can review the guidelines published by the Microsoft Security Response Center.
However, when communication breaks down, some researchers resort to “full disclosure,” releasing the vulnerability details and the proof-of-concept code to the public immediately. This forces the vendor’s hand but simultaneously arms cybercriminals with ready-made weapons.
| Disclosure Method | Industry Impact | Risk to Organizations |
|---|---|---|
| Coordinated Disclosure | Vendors have time to patch software. | Low (Protections are in place before public knowledge). |
| Full Disclosure (No Code) | Forces rapid vendor response. | Medium (Hackers must still engineer the exploit). |
| Full Disclosure (With Code) | Triggers an immediate crisis. | Extremely High (Script kiddies and APTs can attack instantly). |
The “Full Disclosure” Fallout: A Race Against Time
Huntress researchers have observed live attacks leveraging these exact exploits. Because the code was published openly on GitHub, threat actors ranging from sophisticated nation-state hackers to lower-tier cybercriminal gangs do not need to spend time reverse-engineering the vulnerabilities. They simply download the tools and deploy them against targeted corporate environments.
While Microsoft successfully rolled out a patch for the BlueHammer vulnerability earlier this week, IT administrators are scrambling to secure their networks against the remaining UnDefend and RedSun flaws. Microsoft communications director Ben Hope reiterated the company’s stance, emphasizing that coordinated disclosure is vital for supporting customer protection and the security research community safely.
“Scenarios like these cause us to race with our adversaries; defenders frantically try to protect against ill-intended actors who rapidly take advantage of these exploits… especially now as it is just ready-made attacker tooling.”
Protecting Enterprise Networks
For organizations relying heavily on Windows Defender, the coming days are critical. Until Microsoft issues comprehensive patches for UnDefend and RedSun, cybersecurity teams must employ aggressive network monitoring, isolate critical assets, and implement strict least-privilege access controls. This incident serves as a stark reminder of the fragile ecosystem shared by independent security researchers, massive tech corporations, and the businesses that rely on their software to stay secure.
| Immediate Defense Strategies | Action Required by IT Teams |
|---|---|
| Apply Available Patches | Immediately update systems to mitigate the BlueHammer flaw. |
| Monitor Endpoint Logs | Watch for unusual administrative privilege escalations. |
| Isolate Sensitive Networks | Restrict lateral movement capabilities within the corporate environment. |
Frequently Asked Questions
What vulnerabilities are hackers currently exploiting in Windows?
Hackers are currently exploiting three specific flaws found in Windows Defender, which have been named BlueHammer, UnDefend, and RedSun.
Who discovered and leaked these security flaws?
An independent security researcher going by the online alias “Chaotic Eclipse” published the flaws and the exploit code after a dispute with Microsoft.
What does the exploit code allow hackers to do?
The vulnerabilities allow an attacker to gain high-level administrator access to an affected Windows computer, giving them total control over the system.
Has Microsoft fixed these vulnerabilities yet?
Microsoft has released a patch for the BlueHammer vulnerability, but as of this reporting, UnDefend and RedSun remain unpatched.
What is “full disclosure” in cybersecurity?
Full disclosure is when a security researcher publicly releases all technical details and exploit code for a vulnerability before the software vendor has had a chance to patch it.
How did cybersecurity firm Huntress identify the attacks?
Huntress researchers observed hackers actively using the exact exploit code published by Chaotic Eclipse to break into at least one organization’s network.
What should organizations do to protect themselves?
Organizations should immediately apply the patch for BlueHammer, strictly monitor their networks for unauthorized privilege escalation, and await further security updates from Microsoft.
Disclaimer: This article is for informational purposes only. Cybersecurity threats are constantly evolving, and organizations should consult with their IT security professionals and refer to official Microsoft security bulletins for the most current mitigation strategies.