The cybersecurity community is on high alert after recent news broke that cisa adds actively exploited linux root vulnerability CVE-2026-31431 to its Known Exploited Vulnerabilities (KEV) catalog. This critical update from the U.S. Cybersecurity and Infrastructure Security Agency (CISA) underscores a severe, active threat to servers, cloud infrastructures, and enterprise environments running various Linux distributions worldwide. The vulnerability, which has been lurking in the Linux kernel for nearly a decade, provides threat actors with a frighteningly simple method for escalating privileges and seizing complete control over affected machines.
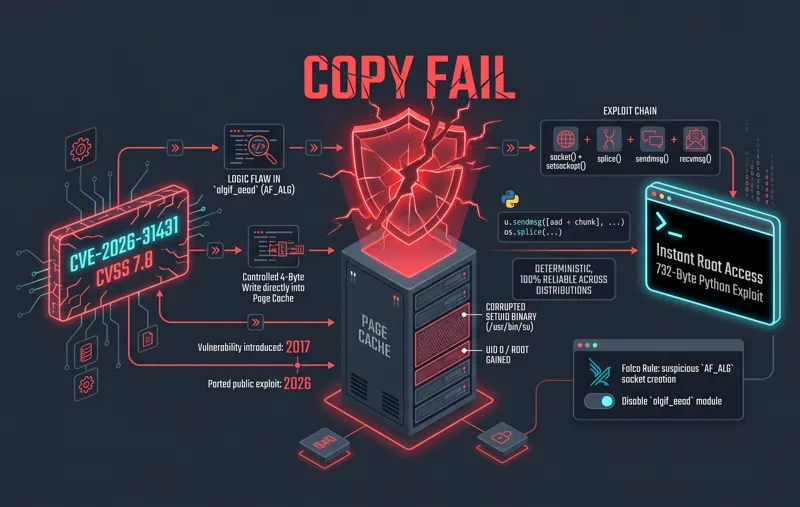
Tracked formally as CVE-2026-31431 and dubbed “Copy Fail” by security researchers at Theori and Xint, this local privilege escalation (LPE) flaw carries a high-severity CVSS score of 7.8. While it requires the attacker to already have a foothold in the system, its reliability and ease of execution make it a goldmine for cybercriminals. By exploiting a logic bug introduced through a series of seemingly harmless kernel updates between 2011 and 2017, unprivileged local users can instantly obtain root-level access. CISA’s decision to mandate immediate remediation highlights the widespread, active exploitation of this flaw in the wild.
Understanding the “Copy Fail” Vulnerability (CVE-2026-31431)
At its core, the Copy Fail vulnerability is a devastating logic bug residing within the Linux kernel’s authentication cryptographic template. According to CISA’s official advisory, the flaw stems from an “incorrect resource transfer between spheres,” which ultimately allows for unauthorized privilege escalation. What makes this vulnerability particularly insidious is its origin. It was not introduced by a single catastrophic coding error, but rather through three separate, individually harmless changes committed to the Linux kernel in 2011, 2015, and 2017. When combined, these changes created a perfect storm for memory corruption.
| Vulnerability Profile | Details |
|---|---|
| CVE Identifier | CVE-2026-31431 |
| Common Name | Copy Fail |
| CVSS Score | 7.8 (High Severity) |
| Vulnerability Type | Local Privilege Escalation (LPE) |
| Root Cause | Logic bug in auth cryptographic template |
The vulnerability impacts any Linux distribution shipped since 2017. It allows a low-privileged user to corrupt the kernel’s in-memory page cache for any readable file, which critically includes setuid binaries. Because the page cache acts as the in-memory representation of executable files, attackers can modify binaries as they execute without ever touching the physical disk. This allows the exploit to completely bypass traditional file integrity monitoring (FIM) systems that only scan for changes on the storage drive.
“Because the page cache represents the in-memory version of executables, modifying it effectively alters binaries at execution time without touching disk. This enables attackers to inject code into privileged binaries and thereby gain root privileges.”
The Mechanics of the Attack: A 732-Byte Nightmare
Security analysts have noted that the barrier to entry for exploiting Copy Fail is astonishingly low. Unlike many modern vulnerabilities that require complex techniques, precise race conditions, or memory address guessing (which can often crash the system if done incorrectly), CVE-2026-31431 can be triggered reliably. Researchers demonstrated that a minuscule 732-byte Python script is all it takes to execute the exploit successfully.
The attack process is stealthy and leverages entirely legitimate system calls, making it incredibly difficult for standard endpoint detection and response (EDR) solutions to distinguish the malicious activity from normal application behavior. The Microsoft Defender Security Research Team has outlined the typical attack path observed during their threat hunting operations.
| Attack Stage | Action Taken by Threat Actor |
|---|---|
| 1. Reconnaissance | Identify a Linux host or container running a susceptible kernel version. |
| 2. Preparation | Deploy the small Python trigger (or Go/Rust variants) to the endpoint. |
| 3. Execution | Run the exploit from a low-privilege context (e.g., compromised container). |
| 4. Memory Corruption | Perform a controlled 4-byte overwrite in the kernel page cache. |
| 5. Escalation | Elevate process to UID 0, securing full administrative root control. |
This streamlined execution chain means that once an attacker gains initial access—perhaps through a stolen SSH key, a misconfigured application, or a compromised CI/CD pipeline—they can achieve total system dominance in a matter of seconds.
A Massive Threat to Cloud and Container Environments
The ubiquity of Linux in modern enterprise architecture, particularly within cloud computing and containerized deployments, exponentially amplifies the danger of CVE-2026-31431. Organizations relying heavily on microservices are at severe risk. Cybersecurity firm Kaspersky provided an in-depth analysis of the flaw, noting that Copy Fail poses a catastrophic risk to containerized environments like Docker, LXC, and Kubernetes.
By default, these containerization technologies grant processes inside a container access to the AF_ALG subsystem if the `algif_aead` module is loaded into the host machine’s kernel. Because containers share the underlying host kernel, a vulnerability of this nature destroys the boundaries that containerization is supposed to provide.
“Copy Fail poses a risk of breaching container isolation and gaining control over the physical machine. At the same time, exploitation does not require the use of complex techniques, which lowers the entry barrier for a potential attacker.”
If a threat actor compromises a single, low-privilege container running a minor microservice, they can use the Copy Fail exploit to break out of that container’s sandbox. Once out, they gain root access to the physical host node, allowing them to compromise all other containers running on that machine, steal secrets, or pivot deeper into the corporate network.
| Environment | Vulnerability Impact |
|---|---|
| Traditional Linux Servers | Full system compromise; unprivileged users become root administrators. |
| Docker & LXC Containers | Sandbox escape; attackers breach isolation to control the underlying host. |
| Kubernetes Clusters | Node compromise; potential to pivot and take over the entire cluster orchestration. |
Active Exploitation and the Urgent May 15 Patch Deadline
The theoretical danger of Copy Fail is alarming, but the practical reality is much worse. The vulnerability is actively being exploited in the wild. While CISA has withheld specific details regarding the exact nature of the active attacks to prevent further proliferation of the tactics, telemetry from major security vendors paints a grim picture. Fully working exploit proofs-of-concept (PoCs) are already circulating widely.
Beyond the original 732-byte Python script, security teams have detected Go and Rust implementations of the exploit within open-source repositories. The Microsoft Defender Security Research Team has observed preliminary testing activity that strongly indicates threat actors are gearing up for a massive wave of exploitation campaigns. The vulnerability requires an initial access vector, but once inside, the damage is immediate.
“Critically, this vulnerability is not remotely exploitable in isolation, but becomes highly impactful when chained with an initial access vector such as Secure Shell (SSH) access, malicious CI job execution, or container footholds.”
In response to the escalating threat, CISA has taken decisive action by adding CVE-2026-31431 to the CISA Known Exploited Vulnerabilities Catalog. Furthermore, a strict directive has been issued to all Federal Civilian Executive Branch (FCEB) agencies: they must apply the available security patches by May 15, 2026. Private organizations and commercial enterprises are strongly urged to adhere to this same deadline to protect their infrastructure from imminent ransomware and data extortion attacks.
| Mitigation Strategy | Action Required |
|---|---|
| Apply Kernel Updates | Upgrade to patched Linux kernel versions 6.18.22, 6.19.12, or 7.0 immediately. |
| Disable Affected Features | If patching is impossible, disable the vulnerable cryptographic subsystem. |
| Implement Network Isolation | Restrict access to critical servers to prevent initial access vectors like SSH brute-forcing. |
| Enhance Access Controls | Audit container privileges and ensure least privilege principles are strictly enforced. |
The clock is ticking. System administrators, DevOps engineers, and security teams must prioritize patching this vulnerability before threat actors automate the exploit and incorporate it into standard malware toolkits. The nine-year run of Copy Fail is over, but the fallout from unpatched systems has only just begun.
Frequently Asked Questions

What is CVE-2026-31431?
CVE-2026-31431 is a high-severity local privilege escalation (LPE) vulnerability in the Linux kernel, also known as “Copy Fail.” It allows an unprivileged local user to gain root access by corrupting the kernel’s in-memory page cache.
Why is it called Copy Fail?
Security researchers at Theori and Xint named it Copy Fail because the flaw involves a logic bug and an incorrect resource transfer within the Linux kernel’s authentication cryptographic template, leading to memory corruption during copy operations.
How does this vulnerability impact Docker and Kubernetes?
It poses a massive risk to containerized environments. Because containers share the host’s kernel, an attacker who compromises a low-level container can use Copy Fail to break container isolation and take full root control of the physical host machine.
Are there patches available for this Linux vulnerability?
Yes, fixes have been released by Linux maintainers. System administrators are urged to update to Linux kernel versions 6.18.22, 6.19.12, or 7.0 to remediate the flaw.
What is the CISA deadline for patching this vulnerability?
CISA has mandated that all Federal Civilian Executive Branch (FCEB) agencies apply the necessary patches for CVE-2026-31431 no later than May 15, 2026. Private businesses are highly recommended to follow the same timeline.
Can CVE-2026-31431 be exploited remotely?
No, it cannot be exploited remotely in isolation. It is a local vulnerability (AV:L), meaning the attacker must first gain some form of low-privileged access to the system (e.g., via compromised SSH keys or a vulnerable web application) before executing the exploit.
How are attackers using this in the wild?
Threat actors are chaining this vulnerability with initial access techniques. Once inside a system or container, they deploy small exploit scripts (written in Python, Go, or Rust) to instantly elevate their privileges to root, allowing them to deploy malware, steal data, or establish persistent backdoors.
Disclaimer: This article is for informational purposes only. The cybersecurity landscape is constantly evolving, and vulnerabilities pose serious risks to digital infrastructure. Always consult official vendor documentation and certified security professionals before applying system patches or altering network configurations.