In a critical update released this week, it was confirmed that apple fixes bug that cops used to extract deleted chat messages from iphones, finally closing a major privacy loophole that has existed for months. For years, privacy-conscious individuals, journalists, and activists have relied on encrypted messaging applications with self-destructing message features to maintain operational security. However, a hidden vulnerability within the iOS operating system ecosystem inadvertently undermined these robust security measures, creating a digital paper trail where none should have existed.
The Mechanics Behind the iOS Notification Flaw
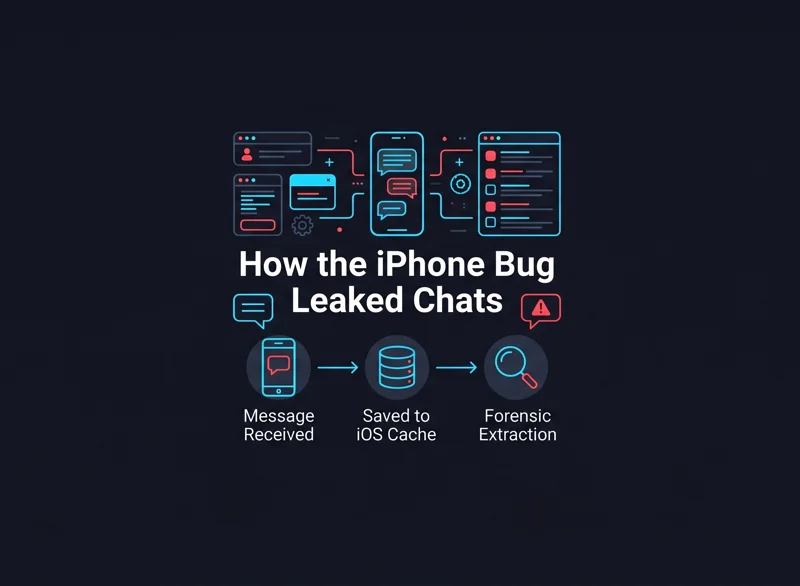
To understand the severity of this issue, it is essential to look at how modern smartphones handle background alerts. When you receive a message on an app like Signal or WhatsApp, the application sends a payload to the iOS notification center to alert you on your lock screen. The core issue was that Apple’s operating system cached these notification payloads in an internal database. Even if a user set their messages to disappear after five minutes within the app itself, the plain-text preview of that message remained securely tucked away in the device’s hidden system files for up to a month.
Forensic experts and law enforcement agencies, including the FBI, discovered this discrepancy. By utilizing advanced mobile forensic extraction tools, authorities could bypass the encrypted application entirely. They simply extracted the iOS notification database, effectively reading the “deleted” conversations through the system’s retained memory.
“Security is only as strong as its weakest link, and in this case, the operating system was quietly preserving the very secrets the application was designed to destroy.”
How Different Apps Handled the Vulnerability
The impact of this bug varied depending on how users configured their applications and whether they allowed message previews on their lock screens. Below is a breakdown of how this affected the ecosystem prior to the patch.
| Messaging App | Disappearing Feature | Vulnerability Status (Pre-Patch) |
|---|---|---|
| Signal | Hardware-level secure deletion | High: Previews were cached by iOS. |
| Configurable auto-delete | High: Subject to the same notification logging. | |
| iMessage | Recently Deleted folder (30 days) | Moderate: Native integration mitigates some cache leaks, but logging still occurred. |
Industry Reaction and Apple’s Swift Response
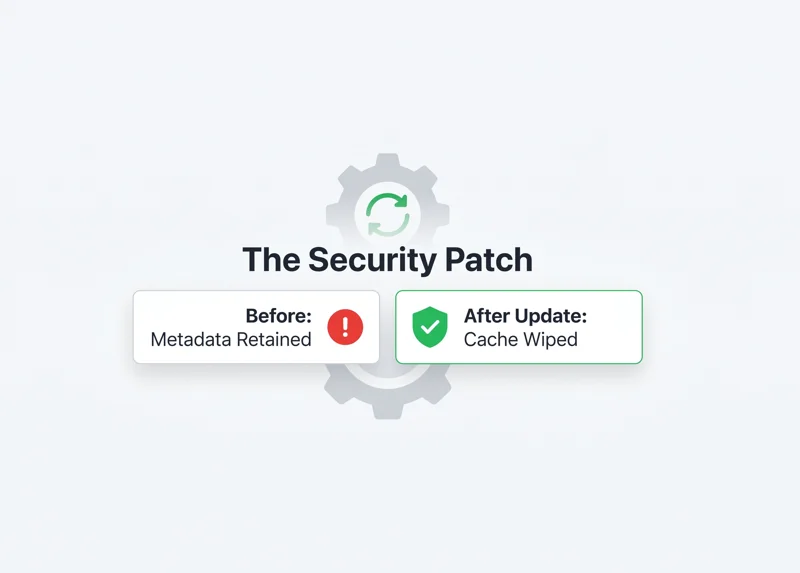
The revelation of this loophole sent shockwaves through the cybersecurity community. Independent news outlets initially broke the story, detailing how forensic analysts were recovering Signal messages that targets believed were permanently erased. Signal’s leadership was quick to respond, actively lobbying Apple to correct the oversight. The argument was straightforward: if an application instructs the operating system to delete a message, all corresponding metadata and notification logs tied to that message should also be purged simultaneously.
In response to the mounting pressure and the clear threat to user privacy, Apple took decisive action. The tech giant released a comprehensive security patch, explicitly addressing the way the notification center handles data lifecycle management. You can read more about Apple’s ongoing commitment to user safety in Apple’s official security notice regarding recent iOS updates.
“Notifications for deleted messages shouldn’t remain in any OS notification database. We are glad to see this standard finally enforced at the system level.”
Timeline of the Exploit Resolution
The journey from the discovery of this forensic loophole to its ultimate resolution highlights the ongoing cat-and-mouse game between device manufacturers, privacy advocates, and law enforcement.
| Phase | Event Description |
|---|---|
| Discovery | Cybersecurity researchers note forensic tools extracting deleted texts via iOS cache. |
| Exposure | Media reports confirm the FBI used this exact method to bypass Signal’s auto-delete. |
| Advocacy | Privacy leaders demand an immediate structural fix to the iOS notification center. |
| Resolution | Apple deploys a software update patching the vulnerability, backported to older iOS 18 devices. |
Why This Fix Matters for At-Risk Users
For the average consumer, a cached notification might seem like a minor technical oversight. However, for at-risk demographics—such as investigative journalists, political dissidents, and human rights activists—this flaw posed a life-threatening risk. These individuals rely on the mathematical certainty of encryption and the absolute guarantee of self-destructing messages to protect their sources and themselves. By ensuring that notifications are now securely purged alongside the parent message, Apple has restored the integrity of secure communications on its platform.
Users are heavily advised to update their devices immediately. While the fix prevents future messages from being logged inappropriately, device owners should also consider power-cycling their phones and clearing old notifications to ensure legacy data is flushed from the system’s memory banks.
Frequently Asked Questions (FAQs)
What exactly was the iPhone notification bug?
It was a flaw where the iOS operating system saved the text of app notifications (like incoming messages) in a hidden database for up to a month, even if the message was deleted inside the app.
How did law enforcement use this bug?
Police and the FBI used forensic software to extract the hidden iOS notification database from seized iPhones, allowing them to read messages that users thought had successfully self-destructed.
Which messaging apps were affected?
Any app that utilizes iOS notifications to display message previews was potentially affected, including highly secure apps like Signal and WhatsApp.
Has Apple fixed this issue completely?
Yes, Apple released a software update that changes how notifications are stored, ensuring that when a message is marked for deletion, its corresponding notification cache is also wiped.
Do I need to buy a new phone to get the fix?
No, the fix was delivered via a standard software update. Apple also backported the security patch to older devices running iOS 18.
How can I protect my messages in the future?
Always keep your device’s operating system updated to the latest version and consider disabling lock screen message previews for sensitive applications.
Did Apple comment on why the data was kept in the first place?
Apple’s security notes indicated it was an unintended bug where notifications “marked for deletion could be unexpectedly retained,” rather than a deliberate surveillance feature.
Disclaimer: This article is for informational purposes only and does not constitute professional cybersecurity or legal advice. Always ensure your devices are updated to the latest firmware to maintain optimal security.