Introduction: Decoding the Text from an Unknown Number
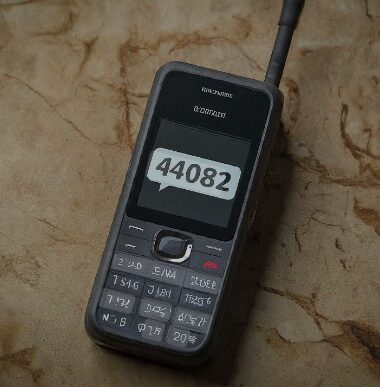
The experience is a common one in the modern digital age: a phone buzzes, revealing a text message not from a friend, family member, or colleague, but from a strange, abbreviated number. These five- or six-digit senders can be a source of both convenience and concern. They deliver flight updates, two-factor authentication codes, and retail promotions, yet they can also be the harbingers of unsolicited marketing, phishing attempts, or outright scams. This ambiguity often leaves consumers questioning the origin, legitimacy, and safety of such communications.
This report centers on an investigation into one such number: the 44082 short code. For any U.S. consumer who has received a message from this specific code, questions naturally arise. Who is behind it? What is its purpose? Is it legitimate? This analysis will treat the 44082 short code as a case study, using it as a key to unlock a deeper understanding of the vast and highly regulated mobile messaging industry that operates behind the scenes in the United States. The inquiry into this single number provides a practical lens through which to examine the entire framework of commercial text messaging.
The objective of this report is to provide a definitive and exhaustive resource for the American consumer. It will begin by deconstructing the anatomy of the legitimate U.S. short code system, explaining what these numbers are, why businesses invest heavily in them, and the strict rules that govern their use. Following this foundational overview, the report will present a direct investigation into the 44082 short code, consulting official registries to determine its status within the United States. Finally, and most critically, this analysis will equip the reader with a comprehensive guide to their rights and the powerful tools available on modern smartphones to manage, block, and report any unwanted messages, thereby transforming uncertainty into empowered action.
The Anatomy of a U.S. Short Code: More Than Just a Number
To accurately assess the nature of a message from a number like the 44082 short code, it is first essential to understand the structure, purpose, and regulation of the legitimate short code ecosystem in the United States. These abbreviated numbers are not random; they are a specialized class of communication tool, acquired and operated under a stringent set of rules designed to facilitate high-volume business messaging while protecting consumers.
What is an SMS Short Code?
At its core, an SMS short code is a five- or six-digit phone number used by businesses and organizations to send and receive text messages at scale. Unlike standard 10-digit phone numbers, which are primarily designed for peer-to-peer (P2P) communication, short codes are engineered for application-to-person (A2P) messaging. This means they are the designated channel for a system or application to send a message to a large number of individuals simultaneously. These numbers are leased, not permanently owned, and their use is dedicated to specific, pre-approved campaigns.
In the United States, the use cases for these short codes are deeply integrated into daily life and can be categorized into several key functions:
- Marketing and Promotions: This is one of the most visible uses. Businesses send subscribers text messages containing special offers, announcements of new products, company news, and alerts for time-sensitive events like flash sales. Consumers typically opt into these campaigns by texting a keyword (e.g., “JOIN”) to the company’s short code.
- Transactional Alerts: Short codes are critical for providing automated, real-time information. This includes order and shipping confirmations from e-commerce retailers, appointment reminders from healthcare providers, and flight status updates from airlines. These messages are functional rather than promotional and are triggered by a specific consumer action.
- Security and Authentication: A vital function of short codes is their role in digital security. When a user logs into a sensitive account, such as online banking, the service can send a one-time passcode via text to a pre-registered mobile number. This process, known as two-factor authentication (2FA), adds a crucial layer of security to prevent unauthorized access.
- Customer Engagement and Interactive Services: Organizations use short codes to foster interaction. This can include television programs asking viewers to vote for a contestant, charities soliciting donations, or brands running contests and sweepstakes where consumers enter by texting a specific code.
The Business Rationale: Why Companies Invest in Short Codes
The acquisition and maintenance of a dedicated short code represent a significant financial and logistical investment for a business, often costing between $500 and $1,000 per month and requiring a lengthy approval process of four to five weeks. The decision to use this channel over less expensive alternatives is driven by several distinct technical and strategic advantages that are unparalleled by other forms of messaging.
- Unmatched Throughput and Speed: The primary advantage of a short code is its message throughput. A provisioned short code is capable of sending over 500 messages per second, a rate that dwarfs the capacity of other number types. This high speed is indispensable for large-scale, time-sensitive communications. For a national retailer launching a four-hour flash sale, the ability to notify millions of customers within minutes is a critical operational capability that directly impacts revenue.
- Superior Deliverability and Reduced Filtering: Before a short code can be used, its intended purpose must be detailed in an application that is submitted to and approved by every major wireless carrier in the United States. This rigorous, upfront vetting process means that messages sent from an approved short code are pre-screened and considered trusted traffic by the carriers. Consequently, these messages are subject to minimal spam filtering, ensuring a much higher deliverability rate compared to other number types that can be flagged or blocked by carrier algorithms. This reliability is paramount for critical communications like 2FA codes, where a blocked message can lock a user out of their account.
- Enhanced Brand Recognition and Trust: A dedicated short code functions as a unique, credible identifier for a business. Over time, consumers learn to recognize and trust messages from a specific number associated with their bank, airline, or favorite retailer. This builds brand equity and reduces the likelihood that a consumer will dismiss a message as spam. This effect is amplified with the use of “vanity” short codes—numbers that are specifically chosen to be memorable or to spell out a relevant word on a phone keypad, such as 32623 for “DANCE”. This memorability makes it easier for consumers to opt into marketing campaigns they see on billboards, hear on the radio, or see in print ads.
The significant cost and lengthy carrier approval process are not merely business hurdles; they function as a crucial, built-in mechanism for consumer protection. This high barrier to entry creates a “gated community” for high-volume messaging in the U.S. The system is financially and administratively designed to filter out transient or ill-intentioned actors who are unwilling or unable to undergo such a rigorous and expensive vetting process. The deliberate phasing out of cheaper, less traceable “shared” short codes further solidified this principle, ensuring that a single, accountable entity is tied to each number. This structure inherently increases the baseline level of trust a consumer can have in a message originating from a verified U.S. short code, as the sender has invested significant resources and submitted to carrier oversight to earn the privilege of using it.
Types of U.S. Short Codes: A Taxonomy
The landscape of U.S. short codes has evolved to prioritize security and accountability. Understanding the types of codes, including one that has been intentionally deprecated, is key to recognizing legitimate messaging practices.
- Dedicated Codes (The Modern Standard): This is the current and only accepted model for short code use in the United States. A dedicated short code is leased by a single company for its exclusive use, ensuring that all messages from that number are attributable to one organization. This exclusivity is the cornerstone of the system’s security and accountability. Dedicated codes come in two varieties:
- Random (Non-Vanity) Codes: When a business applies for a new short code without a specific number preference, a random five- or six-digit number is assigned to them. This is the more common and cost-effective option, with leasing fees typically starting around $500 per month.
- Vanity Codes: For an additional premium—often bringing the monthly cost up to $1,000—a business can choose a specific, easy-to-remember number. Much like a vanity license plate, these codes are selected for their mnemonic value (e.g., 222444) or their ability to spell a word, enhancing brand recall and making it simpler for consumers to engage with marketing campaigns.
- The End of an Era: The Phase-Out of Shared Short Codes: In the past, a more affordable option existed where multiple businesses could use the same short code, differentiating their campaigns with unique keywords. However, this model presented a significant challenge for regulation and spam control. If a malicious entity sent fraudulent messages from a shared code, it was difficult for carriers to isolate and penalize the specific offender without disrupting service for all other legitimate businesses using that same number. Recognizing this security risk, major U.S. wireless carriers began to ban the use of shared short codes in 2021, compelling businesses to migrate to dedicated numbers. This policy shift was a critical step in bolstering the integrity and trustworthiness of the A2P messaging ecosystem.
To provide a clearer context, the following table compares the key attributes of the three primary types of numbers used for business messaging in the United States.
Data synthesized from.
This comparison illustrates the deliberate trade-offs businesses make when choosing a messaging channel. While 10DLC and toll-free numbers are faster to set up and far less expensive, they cannot match the sheer speed and deliverability of a dedicated short code. The choice to invest in a short code is a strategic decision made by organizations that require the highest level of performance and reliability for mass communication.
The Investigation into the 44082 Short Code
With a clear understanding of how the legitimate U.S. short code system is structured, it is now possible to conduct a methodical and conclusive investigation into the 44082 short code. This process involves consulting the official, authoritative sources that govern the use of these numbers in the United States.
The Official Search: Consulting the U.S. Short Code Registry
In the United States, the management of all Common Short Codes (CSCs) is centralized. The CTIA (Cellular Telecommunications Industry Association), a trade association representing the U.S. wireless communications industry, oversees the official U.S. Short Code Registry. This registry is the single source of truth for identifying the lessee of any given short code and is publicly accessible through the website usshortcodes.com. This transparency is a key feature of the regulated system, allowing consumers, businesses, and regulators to verify the ownership of a number.
The process for looking up a short code is straightforward. The registry’s website provides a search function where any five- or six-digit number can be entered. If the code is leased and active in the U.S., the directory will provide information about the company that leases it. This lookup capability is the primary tool for verifying the legitimacy of a short code sender.
A comprehensive search for the 44082 short code was conducted using the official U.S. Short Code Directory. The definitive finding of this search is that the number 44082 short code is not currently available or registered within the U.S. system. The registry returns no results for this number, confirming that it is not an active, carrier-approved Common Short Code in the United States.
Interpreting the Absence: What Does “Not Found” Mean?
The fact that the 44082 short code does not appear in the official U.S. registry is a critical piece of information with several important implications.
The primary conclusion is that this number is not authorized to send A2P (application-to-person) messages through the official, regulated channels used by major brands and organizations in the United States. It operates outside the purview of the CTIA’s guidelines and the oversight of U.S. wireless carriers. This immediately raises questions about the origin and intent of any messages sent from it. Several possibilities can explain its appearance on a U.S. consumer’s phone:
- Non-U.S. Origin: Short code systems are country-specific. A short code leased in the United States is not valid in Canada or Europe, and vice versa. The most likely explanation is that
44082 short code is a valid short code in a different country, and messages from it are being routed internationally to U.S. phones. Publicly available, user-reported data, though not official, indicates message activity for this number associated with locations such as Sierra Leone and the U.S. Virgin Islands. This suggests the messages are originating from outside the mainland U.S. telecommunications infrastructure.
- Spoofing or Illegitimate Sender: The sender ID of a text message can sometimes be “spoofed,” or falsified, to mask the true origin of the message. It is possible that the messages do not originate from a legitimate service using the number 44082 at all, but rather from a malicious actor using technical means to make it appear as if they are. This is a common tactic in phishing campaigns, where scammers impersonate legitimate entities to trick recipients into revealing sensitive information.
- Non-Standard Messaging Service: A less likely but possible explanation is that the number belongs to a non-standard Voice over IP (VoIP) or over-the-top (OTT) messaging service that does not interface with the traditional carrier-based short code system.
The query into this single, unregistered number exposes a fundamental dynamic of the global messaging network: the tension between robust national regulation and seamless international interoperability. A U.S. consumer’s mobile phone is, by its nature, a global endpoint capable of receiving messages from nearly anywhere in the world. The CTIA’s highly structured and verifiable registry creates a secure and well-regulated environment for domestic A2P messaging. However, this domestic system cannot erect a firewall against messages that originate from international systems, which may operate under entirely different and often less stringent regulatory standards. This creates a “regulatory seam” at the borders of the U.S. network. Spammers and malicious actors can exploit this seam, sending messages from less-regulated jurisdictions into the U.S. This explains the apparent paradox: a consumer can be in a country with one of the world’s most controlled short code systems and still receive suspicious, untraceable texts from a number like 44082 short code. The issue is not a failure of the domestic system, but an inherent vulnerability of a globally interconnected communications grid.
Conclusion of the Investigation
Based on a thorough review of the official U.S. short code infrastructure, the 44082 short code is not a registered, carrier-approved entity for business or organizational mass communication within the United States. Any message received from this number by a U.S.-based consumer should be treated with extreme caution. Its absence from the official registry means it operates outside the established consumer protection frameworks that govern legitimate U.S. short code campaigns. Specifically, there is no guarantee that it will honor standard opt-out commands (like STOP) or provide sender information upon request (via a HELP command), which are mandatory for all compliant U.S. programs.
Your Rights and Tools: A Consumer’s Guide to Managing Short Code Messages
Receiving an unsolicited message from an unverified number like the 44082 short code can be unsettling, but consumers are not powerless. The U.S. messaging ecosystem includes a set of consumer rights, and modern smartphones are equipped with powerful tools to manage, filter, and block unwanted communications. Understanding these rights and tools provides a clear path from passive reception to active control over one’s digital inbox.
The Language of Compliance: Universal Commands
For all legitimate short code programs operating within the United States, the CTIA’s Short Code Monitoring Handbook outlines a set of mandatory keywords that empower consumers to control the messages they receive. These commands are a consumer’s first line of defense and a simple test of a sender’s legitimacy.
Data synthesized from.
- The Power of “STOP”: The most critical command is STOP. By law and industry standard, any legitimate short code campaign must recognize this keyword and immediately add the user’s number to an opt-out list. After sending “STOP,” the user should receive one final confirmation message, and no further messages should be sent unless the user explicitly opts back in.
- The Family of Opt-Out Keywords: The system is designed to be user-friendly and recognizes several variations of the opt-out command. The keywords UNSUBSCRIBE, CANCEL, END, and QUIT must also be honored in the same manner as STOP. This ensures that consumers can unsubscribe easily using natural language.
- The “HELP” Command: If a consumer is unsure about the identity of a short code sender, they have the right to text HELP to that number. A compliant service is required to respond with its name and customer care information, such as a toll-free number or website address. This provides a direct path for the consumer to identify the company behind the messages and seek further assistance. A failure to respond to HELP is a significant red flag indicating a non-compliant or illegitimate sender.
Proactive Defense: Blocking and Filtering on Your Smartphone
In situations involving a number like the 44082 short code, which operates outside the U.S. compliance framework, sending “STOP” may have no effect. In these cases, the most effective strategy is to shift from asking the sender to stop to forcing them to stop at the device level. Both iOS and Android operating systems provide robust, built-in tools for this purpose.
Step-by-Step Guide for iPhone Users
- Blocking a Number Directly: This is the most direct method to prevent a specific number from contacting the user again.
- Open the Messages app and navigate to the conversation from the number to be blocked.
- Tap on the number or contact name at the top of the screen.
- Tap the “Info” button.
- On the next screen, scroll down and tap “Block this Caller.”
- A confirmation prompt will appear. Tap “Block Contact” to finalize the action.
Messages from a blocked number are not delivered, and the sender receives no notification that they have been blocked.
- Filtering Unknown Senders: This feature is designed to reduce inbox clutter and prevent notifications from numbers not in the user’s contacts.
- Go to the Settings app and select “Messages.”
- Scroll down to the “Message Filtering” section.
- Toggle on the “Filter Unknown Senders” option.
When enabled, this creates a new “Unknown Senders” tab within the Messages app. All messages from numbers not in the contact list will be routed to this folder, and the user will not receive notifications for them.
- Reporting Junk/Spam: Reporting spam helps Apple and the wireless carriers improve their network-wide filtering capabilities.
- In the Messages app, find the unwanted message in the conversation list.
- If the message has not been opened, swipe left on the message, tap the trash can icon, and then tap “Delete and Report Junk”.
- If the message has already been opened, a “Report Junk” link may appear at the bottom of the conversation. Tapping this link will allow the user to delete the message and report it simultaneously.
Step-by-Step Guide for Android Users
The exact steps for blocking messages on Android can vary slightly depending on the phone’s manufacturer and the specific messaging app being used. However, the general process is consistent across most modern devices.
- Blocking a Number Directly:
- Open the default messaging app (e.g., Google Messages) and open the conversation from the number to be blocked.
- Tap the three-dot menu icon in the top-right corner of the screen.
- Select “Details” from the dropdown menu.
- On the next screen, tap “Block & report spam”.
- A pop-up will appear, giving the option to simply block the number or to also report it as spam to Google and the carrier. Check the box if desired and tap “OK” to confirm.
- Using Built-in Spam Protection: Google’s Messages app includes a powerful, automated spam protection feature that is typically enabled by default. Users can verify its status by navigating to the app’s settings, selecting “Spam protection,” and ensuring the “Enable spam protection” toggle is on. This feature can automatically detect and move suspected spam messages to a separate folder, preventing them from cluttering the main inbox.
Escalation and Further Protection

Beyond device-level controls, consumers can take additional steps to combat unwanted messages and protect their information.
- Reporting to Carriers via 7726 (SPAM): All major U.S. wireless carriers (including AT&T, Verizon, and T-Mobile) support a universal reporting system. A user can forward any suspicious or spam text message to the short code 7726 (which spells SPAM on a keypad). The carrier will then reply with an automated message asking for the original sender’s number. This reporting mechanism provides carriers with valuable data to identify and block malicious senders at the network level, protecting all of their customers.
- Third-Party Applications: A market of third-party applications exists to provide more advanced call and text filtering. Apps like Truecaller and Hiya can identify and block known spam numbers by referencing a large, community-sourced database. While these apps can be effective, it is crucial for consumers to be aware of the privacy implications. To function, these services often require extensive permissions, including access to the user’s contact list and call logs. It is imperative to carefully review the privacy policy of any such app before installation.
The investigation into the 44082 short code serves as a powerful illustration of the modern messaging landscape. The analysis concludes that this number is not a registered, carrier-approved U.S. short code and any messages received from it should be handled with significant caution. This specific finding, however, is secondary to the broader principles it reveals. The case of the 44082 short code highlights the critical distinction between the highly regulated, transparent, and accountable domestic short code system in the United States and the less-regulated channels through which international or unsolicited messages can arrive.
This report has demonstrated that while the digital world presents challenges like unsolicited texts, consumers are equipped with a robust set of rights, tools, and knowledge to protect themselves. The key principles for maintaining digital safety and a clutter-free messaging experience are clear:
- Trust but Verify: The existence of the public U.S. Short Code Directory is a powerful tool for transparency. Consumers should be encouraged to use this resource to verify the legitimacy of unfamiliar short codes, transforming suspicion into certainty.
- Know Your Rights: The universal commands of STOP and HELP are not mere suggestions; they are mandated consumer rights within the legitimate U.S. system. Understanding and using these commands is the primary method for controlling communications from compliant businesses.
- Use Your Tools: For messages that originate outside the compliant system, the blocking and filtering tools built directly into every modern smartphone are the ultimate line of defense. These features provide an immediate and effective way to silence unwanted senders and declutter the digital environment.
Ultimately, the challenge of unsolicited messages is not insurmountable. By understanding the systems that govern legitimate communication and by confidently employing the tools designed for personal protection, any consumer can navigate the messaging world not with apprehension, but with the assurance that they are in full control of their digital domain.
